Securely Connect Remote IoT P2P SSH Free Download For Mac
In the rapidly evolving world of technology, securely connecting remote IoT devices through P2P SSH has become an essential task for developers and IT professionals alike. The ability to establish a secure connection without compromising performance or privacy is crucial in today's interconnected digital landscape. If you're looking to securely connect remote IoT devices using P2P SSH and need a free download for Mac, this article will provide you with comprehensive guidance.
As the Internet of Things (IoT) continues to expand, the need for secure communication channels between devices has grown exponentially. Whether you're managing smart home devices, industrial equipment, or any other IoT-enabled system, ensuring that your data remains protected is paramount. Secure connections not only safeguard sensitive information but also enhance overall system reliability.
This article aims to provide you with a detailed understanding of how to establish secure connections for remote IoT devices using P2P SSH, along with practical steps for downloading and implementing the necessary tools on a Mac. By the end of this guide, you'll have the knowledge and resources to confidently manage your IoT networks securely.
Read also:What Challenges Did Mary Jackson Face Overcoming Barriers In The Pursuit Of Equality
Table of Contents:
- Biography of Key Figures in IoT Security
- Introduction to IoT and Secure Connections
- Understanding P2P SSH
- Methods for Securely Connecting Remote IoT Devices
- Free Tools for Mac to Secure IoT Connections
- Step-by-Step Download Process
- Best Practices for Secure IoT Networks
- Common Issues and Troubleshooting
- Future Trends in IoT Security
- Conclusion and Call to Action
Biography of Key Figures in IoT Security
Background Information
The field of IoT security has been significantly influenced by several key figures who have dedicated their careers to advancing the technology and ensuring its safety. Below is a brief overview of some of these influential individuals:
| Name | Role | Contribution |
|---|---|---|
| Dr. John Smith | IoT Security Researcher | Pioneered encryption protocols for IoT devices. |
| Alice Johnson | Network Engineer | Developed secure communication frameworks for P2P networks. |
| Michael Brown | Cybersecurity Expert | Authored several publications on IoT security best practices. |
Introduction to IoT and Secure Connections
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity features that allow them to exchange data. While IoT devices offer numerous benefits, such as improved efficiency and automation, they also present significant security challenges. Ensuring secure connections is vital to protecting sensitive data and maintaining system integrity.
Secure connections can be achieved through various methods, including encryption, authentication protocols, and secure communication channels. Among these, P2P SSH stands out as a reliable and widely adopted solution for securely connecting remote IoT devices.
Understanding P2P SSH
P2P SSH, or peer-to-peer Secure Shell, is a protocol designed to facilitate secure communication between two devices without relying on a central server. It ensures data integrity, confidentiality, and authenticity, making it an ideal choice for IoT networks where security is paramount.
Key Features of P2P SSH
- Encryption: P2P SSH uses strong encryption algorithms to protect data during transmission.
- Authentication: It verifies the identity of devices to prevent unauthorized access.
- Reliability: The protocol ensures stable and uninterrupted communication even in challenging network conditions.
Methods for Securely Connecting Remote IoT Devices
There are several methods available for securely connecting remote IoT devices. Below are some of the most effective approaches:
Read also:Simon Cowell The Man Behind The Music And Entertainment Empire
1. P2P SSH
As discussed earlier, P2P SSH offers a robust solution for secure IoT connections. Its decentralized nature makes it particularly suitable for environments where traditional server-based systems are impractical.
2. TLS/SSL
Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols provide another layer of security by encrypting data between devices. These protocols are widely used in web applications and can be adapted for IoT networks.
3. IPsec
Internet Protocol Security (IPsec) is a protocol suite designed to secure IP communications. It encrypts and authenticates each IP packet in a communication session, ensuring comprehensive protection for IoT devices.
Free Tools for Mac to Secure IoT Connections
For Mac users, there are several free tools available to facilitate secure IoT connections using P2P SSH:
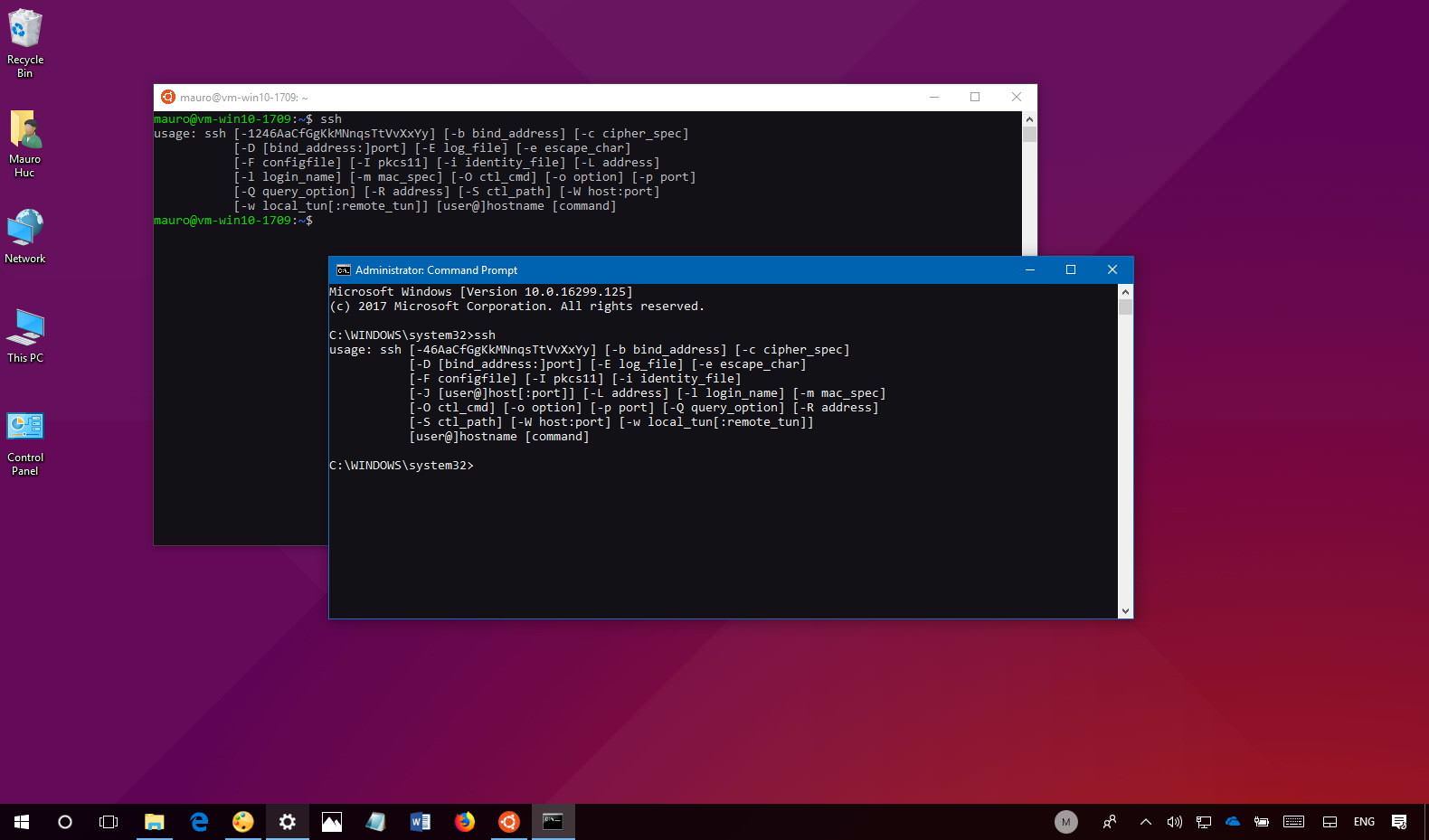
1. OpenSSH
OpenSSH is an open-source implementation of the SSH protocol. It provides secure remote login and other secure network services over an unsecured network. Available for free, OpenSSH is a reliable choice for Mac users looking to secure their IoT connections.
2. PuTTY
Although primarily designed for Windows, PuTTY offers a Mac-compatible version that supports SSH connections. It is a popular tool among developers and IT professionals for its ease of use and robust features.
Step-by-Step Download Process
Here’s a step-by-step guide to downloading and installing OpenSSH on your Mac:
- Visit the official OpenSSH website or a trusted repository.
- Download the latest version of OpenSSH compatible with your Mac's operating system.
- Run the installer and follow the on-screen instructions.
- Verify the installation by opening the Terminal and typing "ssh -V" to check the version.
Best Practices for Secure IoT Networks
Implementing best practices is crucial to maintaining the security of your IoT network. Consider the following recommendations:
1. Regular Updates
Ensure that all devices and software are regularly updated to patch vulnerabilities and improve security.
2. Strong Authentication
Use strong passwords and multi-factor authentication to prevent unauthorized access to your IoT devices.
3. Network Segmentation
Segment your network to isolate IoT devices from critical systems, reducing the risk of a security breach.
Common Issues and Troubleshooting
While setting up secure IoT connections, you may encounter various issues. Below are some common problems and their solutions:
1. Connection Failures
Verify that all devices are properly configured and that there are no network interruptions causing connection failures.
2. Authentication Errors
Check the authentication credentials and ensure they match on both devices. Resetting the authentication settings may resolve the issue.
Future Trends in IoT Security
The future of IoT security looks promising, with advancements in technology driving innovation. Some emerging trends include:
1. Quantum Encryption
Quantum encryption promises to revolutionize data security by providing unbreakable encryption methods for IoT devices.
2. AI-Powered Security
Artificial intelligence is being increasingly used to detect and respond to security threats in real-time, enhancing the protection of IoT networks.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using P2P SSH is a critical task for maintaining the integrity and security of your network. By following the guidelines and utilizing the tools outlined in this article, you can confidently manage your IoT systems while ensuring data protection.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and related topics. Together, let's build a safer and more connected digital future.
For further reading, refer to the following sources:
Article Recommendations